Core Knowledge
There are three different areas of core knowledge that best describe what I learned while in this course, and they are as follows: Attack Surfaces and Controls, Understanding Threats to Identity Access Management Infrastructure Security, and Incident Preparation and Investigation.
Core Knowledge #1
Attack Surfaces and Controls
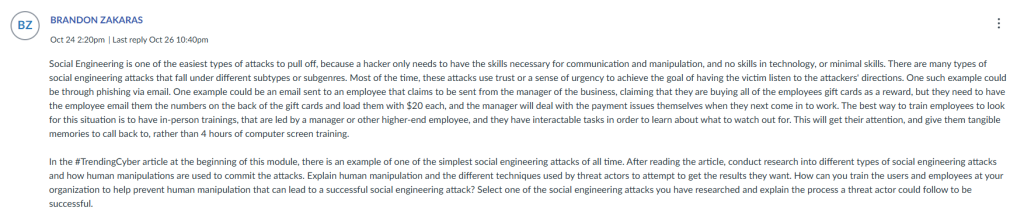
For the first week in this course, the focus was on different attack surfaces, or avenues that attackers will take in order to go after a victim, and how to understand where these avenues may be and prevent them, via controls. For example, one of the largest attack surfaces still in use today is social engineering, and there are many sub types within this surface. There is phishing, which is sending a message that pretends to be from a trusted source in order to convince the victim to commit an action that will open themselves up for an attack. The reason that this type of attack is so popular is because it goes after the person, and not the machine, and people are easier to trick when made anxious than machines. Some controls that can protect information in the physical world are Faraday cages, which are containers that prevent electromagnetic fields from going in or out of the container, protecting it from that type of attack. Locks and sensors are also important controls, and infrared and ultrasonic sensors can be used for different environments. An example of an assignment that was done within this topic was a discussion board centered around the types of training that could be used to help prevent social engineering attacks from being as successful. Here is an example from that assignment.
Core Knowledge #2
Understanding Threats to Identity Access Management Infrastructure Security
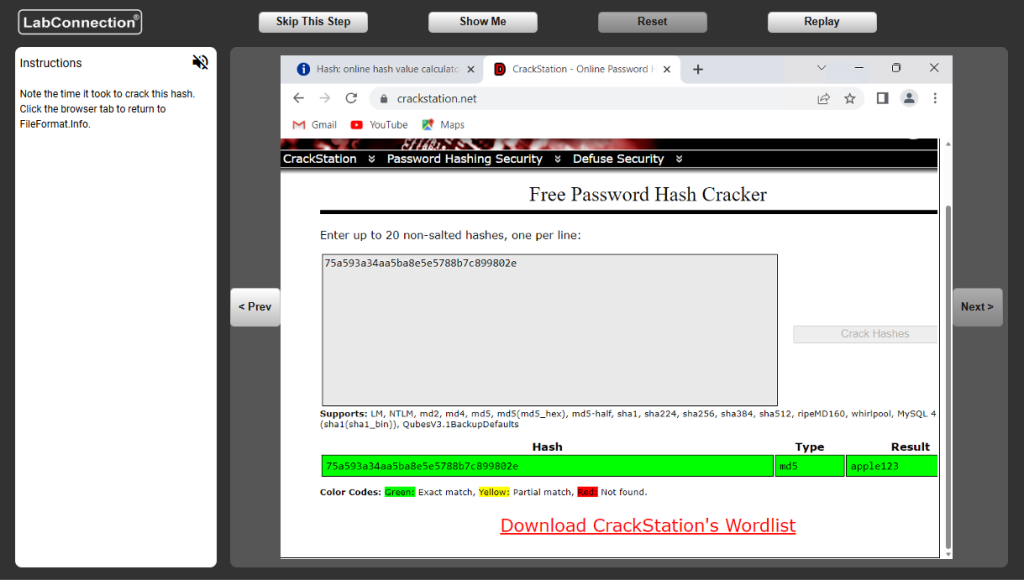
During this topic of the course, there were lessons about the IAM, or Identity Access Management Infrastructure, and how it involves passwords. We learned the different techniques that are used to break password encryptions, and in one of the labs, we were actually tasked with creating a hash for a password and then using a de-hashing website to break back down the hash into its plaintext form, able to be read by people. This was a fun exercise for me, as even though I understand the idea of breaking password hashes, I rarely have the opportunity to practice doing it. A screenshot from this assignment is below.
Core Knowledge #3
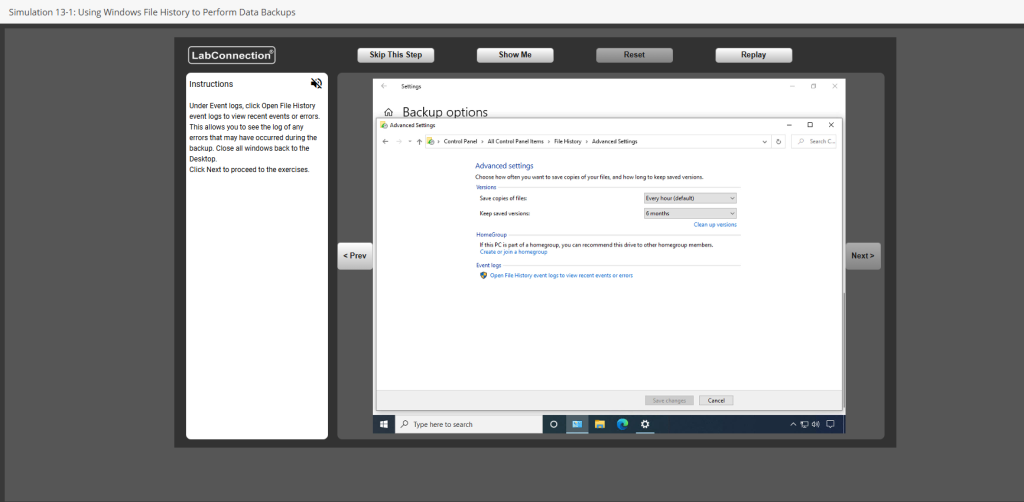
Incident Preparation and Investigation
This topic was especially interesting to me because it is something I have not had a lot of experience with. In fact, I recently, as of December of 2025, had to wipe my entire personal device due to a system corruption that forced my entire computer to be unable to run. If I had known how to do incident preparedness on my own device, I would have been able to prevent such a tragedy. One of the assignments centered around using Windows File History to perform data backups. This was an incredibly interesting assignment to me, as I was able to see how to back up my own device on a consistent basis on an external drive and ensure that my device can be recovered in the future. Below is a screenshot from that assignment.