Reflection Paper 1:
As I completed my first 50 hours at Serco as an intern, I have had the opportunity to apply my cybersecurity knowledge in a professional setting and develop new skills. This experience has not only reinforced my technical abilities but has also provided insight into project management, security compliance, and document control. One of the most significant projects I worked on was generating a SharePoint website for the Sea 04X Program. This task required careful planning, and an understanding of user needs to ensure that the platform improved efficiency. By streamlining supervisory reviews and implementing revision control for contract-critical documents, I helped enhance document traceability and reduce errors. This project enabled me to witness firsthand how digital tools can enhance workflow efficiency in a government contracting environment. It also reinforced the importance of meticulous documentation and version control in maintaining security and operational integrity.
Additionally, I assisted a Security Specialist in performing safety checks to verify compliance with security protocols for the Navy’s critical documents. This process involved conducting audits and maintaining documentation for classified materials, ensuring that all security measures were properly followed. This responsibility emphasized the significance of cybersecurity policies and procedures in safeguarding national defense information. It also deepened my appreciation for the diligence required in handling sensitive materials and the meticulous record-keeping necessary to meet compliance standards. Through these tasks, I have made meaningful progress toward my learning objectives, particularly in developing technical proficiency, understanding security compliance, and improving project management skills. These experiences have also presented challenges, such as adapting to a fast-paced environment where accuracy is crucial and learning to navigate security protocols effectively. However, overcoming these challenges has enhanced my problem-solving abilities and reinforced my commitment to continuous learning in the cybersecurity field.
Reflection Paper 2:
As I complete my second set of 50 hours at Serco as a cybersecurity intern, I have continued to deepen my understanding of real-world cybersecurity practices and expand my professional skill set. During this period, I had the opportunity to work closely with the IT support team on vulnerability management and network security monitoring. This involved assisting in the weekly review of system logs using Splunk and identifying potential threats or unusual activity that could indicate breaches or insider threats. Through this task, I gained practical experience with security information and event management (SIEM) tools, which enhanced my ability to identify early warning signs and respond to security incidents.
Another significant task I contributed to was updating and reviewing the organization’s internal cybersecurity awareness training modules. This included revising outdated content, integrating current phishing tactics, and ensuring that the materials aligned with the Department of Defense (DoD) cybersecurity standards. Participating in this initiative helped me better understand the human aspect of cybersecurity and the importance of ongoing education in building a security-conscious workplace culture. I was also involved in developing a checklist for routine system audits and backups, which will serve as a resource for future interns and full-time employees. This required a clear understanding of system architecture and backup policies. By drafting these materials, I improved my technical writing and documentation skills, while contributing to the team’s goal of maintaining data integrity and business continuity.
This phase of my internship presented new challenges, such as learning to interpret complex log files and understanding network topology diagrams. I often had to troubleshoot under time constraints, which pushed me to become more efficient in using available tools and resources. Collaborating with cross-functional teams also strengthened my communication and teamwork skills, especially when translating technical concepts into accessible terms for non-technical staff.
Overall, these experiences have been invaluable in reinforcing the theoretical knowledge I have gained through coursework. They have allowed me to apply cybersecurity principles in a hands-on environment and underscored the importance of proactive defense strategies, clear documentation, and continuous professional development. As I continue this journey, I’m focused on using what I’ve learned to become a skilled and flexible cybersecurity professional.
Reflection Paper 3:
Name of Interviewee: Kenneth Studley
Position: Information System Security Officer (ISSO), Serco Inc.
Date of Interview: April 17, 2025
For one of my 50-hour reflective journal entries, I chose to interview Kenneth Studley, the Information System Security Officer (ISSO) at Serco, where I am currently completing my internship. I selected Mr. Studley because of his deep experience in cybersecurity compliance and his critical role in maintaining the security and integrity of systems within the organization. His position involves oversight of federal cybersecurity standards and coordination between technical teams and auditors, making him a valuable source of knowledge and insight into both the technical and policy aspects of the cybersecurity field.
When asked how he got into the cyber/IT field and his current position, he shared that his journey began with a background in computer science, which he built upon during his time in the military. His work in military IT roles sparked an interest in cybersecurity, particularly in risk management and system security. After transitioning to civilian life, he took on positions related to compliance and information assurance, gradually progressing into more senior roles that eventually led to his current position as ISSO. His experience in both hands-on technical work and policy enforcement helped him succeed in managing information system security from a high-level perspective. According to him, the most important knowledge, skills, and abilities needed in this field include a strong understanding of cybersecurity frameworks such as the NIST Risk Management Framework (RMF) and FISMA. He emphasized that ISSOs need to understand how to assess system risks, develop and manage security plans, and ensure that systems meet all regulatory compliance requirements. Critical thinking, attention to detail, and the ability to interpret and apply security controls are essential for success in this position. He also pointed out that the cybersecurity field is constantly evolving, so staying current on standards and best practices is key.
When discussing soft skills, he highlighted the importance of communication and collaboration. As an ISSO, he works closely with system engineers, program managers, and external auditors, which requires the ability to clearly explain security requirements and influence others to maintain compliance. He mentioned that leadership, organization, and time management are also critical in juggling multiple security packages and project deadlines. The ability to stay calm under pressure and manage competing priorities is especially valuable in high-stakes or deadline-driven environments. In terms of technical skills, he explained that while ISSO’s role is more policy- and documentation-oriented, a foundational understanding of IT infrastructure is still crucial. Skills related to network architecture, system vulnerabilities, and common tools like Nessus, STIG Viewer, and eMASS are important for assessing risks and overseeing the implementation of proper safeguards. He noted that having hands-on familiarity with these tools helps ISSOs better communicate with technical teams and ensure that systems meet all required controls and standards. When asked about good entry-level jobs that would help someone work toward becoming an ISSO, he recommended beginning in roles like help desk technician, junior system administrator, or IT support specialist. These positions offer the technical foundation needed to understand how systems operate. From there, transitioning into roles such as security analyst or compliance analyst can provide exposure to security assessments, documentation, and risk management frameworks. He emphasized that aspiring ISSOs should seek out experience working on Authorization to Operate (ATO) packages, system security plans, and audits to gain the knowledge and credibility needed for the role.
Final Paper:
Date: April 18, 2025
Name: Sripragna Aditha
Employer: Serco North America
Company/Agency: Serco
Internship Class: CYSE 368
Term: Spring 2025
Table of Contents:
Introduction
Company Overview and Internship Onboarding
Management Environment
Major Work Duties and Projects
Application of Cybersecurity Skills and Knowledge
Academic Preparation and Skill Alignment
Evaluation of Learning Objectives
Most Motivating Aspects
Most Discouraging Aspects
Most Challenging Aspects
Recommendations for Future Interns
Conclusion
Introduction:
Internships serve as a bridge between academic theory and hands-on practice, particularly in dynamic and high-stakes fields like cybersecurity. As a student majoring in cybersecurity at Old Dominion University, I was eager to experience how theoretical concepts like encryption, secure communication, risk analysis, and compliance are applied in real-world environments. After researching various potential internship opportunities, I chose to apply for a role with Serco North America, a decision driven by both professional interest and alignment with my long-term goals.
Serco is a globally recognized government services provider that delivers essential support to defense, intelligence, civilian, and space agencies. With its strong presence in North America and close partnerships with U.S. federal agencies, Serco has established itself as a trusted organization for mission-critical operations, including cybersecurity. I was particularly drawn to Serco because of its comprehensive and evolving cybersecurity services. The company supports various federal programs and infrastructure protection efforts, making it an ideal place to gain firsthand experience in high-impact cybersecurity tasks.
My primary motivation for choosing this internship stemmed from a desire to move beyond the classroom and interact with real security tools, frameworks, and threats. While my coursework provided foundational knowledge in areas such as network security, cryptography, and ethical hacking, I knew that hands-on application in a workplace would deepen my understanding. I wanted to experience how cybersecurity professionals handle live environments, prioritize incidents, perform audits, and ensure compliance with government standards like NIST (National Institute of Standards and Technology) and RMF (Risk Management Framework).
Before beginning the internship, I set three specific learning objectives I hoped to achieve:
- Apply encryption and secure communication techniques to support the protection of sensitive data and systems within real-world environments. This objective focused on strengthening my practical understanding of confidentiality, integrity, and availability through hands-on technical tasks.
- Gain hands-on experience with cybersecurity risk management and incident response, especially within an organization that supports U.S. federal agencies. I wanted to understand how risks are identified, prioritized, mitigated, and reported. These skills are crucial in today’s digital threat landscape.
- Improve my ability to collaborate and communicate effectively in a professional setting. This included learning how to document work, participate in team meetings, coordinate projects with cross-functional teams, and interact with mentors and supervisors in a structured environment.
This paper reflects on my experience during the Spring 2025 internship term, discusses the responsibilities I undertook, and evaluates how this internship shaped both my understanding of cybersecurity and my career path. From the onboarding process to project execution and team collaboration, each section of this paper will demonstrate how my role as a Cybersecurity Engineer Intern at Serco helped me grow professionally and academically.
This internship helped me grow a lot, not just as a cybersecurity student, but also as someone starting in the professional world. I got real hands-on experience and learned a lot from the people I worked with. The support, guidance, and resources I received at Serco boosted my confidence and improved my technical skills. I also started to see myself more clearly as a future cybersecurity professional. In this paper, I will share what I did and learned during my internship, and I hope it helps other students who are thinking about doing something similar.
Company Overview:
Founded in the United Kingdom, Serco Group plc is a global service provider that operates in more than 30 countries. Its North American division, Serco Inc., is headquartered in Herndon, Virginia, and serves primarily federal, state, and local government agencies across the United States. Serco supports a wide variety of sectors, including defense, transportation, healthcare, immigration, and public safety. Its key service offerings in North America include IT and cybersecurity solutions, logistics and supply chain management, engineering, intelligence support, and citizen services.
Serco has built a strong reputation for delivering mission-critical solutions to some of the most sensitive and high-security clients in the country, including the Department of Defense (DoD), Department of Homeland Security (DHS), and Federal Aviation Administration (FAA). The company’s cybersecurity team plays an essential role in ensuring that the digital infrastructure used by these agencies remains secure, functional, and compliant with federal regulations.
I was especially drawn to Serco because of its role in supporting federal systems and infrastructure that affect national security. Working at Serco meant I would not only be learning technical skills but also gaining experience in a work culture shaped by responsibility, confidentiality, and regulatory compliance. These were values that I wanted to develop in myself as a cybersecurity professional.
I joined Serco in October 2024 as a Cybersecurity Engineer Intern. The onboarding process began with a virtual orientation and several days of in-depth security briefings, policy reviews, and training modules. During the first week, I was introduced to Serco’s internal systems and platforms, company policies, workplace conduct expectations, and the cybersecurity tools and protocols I would use.
My orientation included modules on:
- Data protection and privacy policies
- Cybersecurity compliance standards (NIST, FISMA)
- Secure communication protocols
- Workplace conduct and ethical behavior
- Remote access security and multi-factor authentication tools
I also received basic training on Serco’s internal reporting tools, issue-tracking systems, and standard documentation practices. Since many of Serco’s clients are federal agencies, confidentiality and secure communication were heavily emphasized. During the first few days, I was also assigned a mentor, a full-time Cybersecurity professional who helped guide me through daily responsibilities, answered my questions, and reviewed my work during the early weeks of the internship. My first impression of the company was overwhelmingly positive. Everyone I interacted with was welcoming, helpful, and professional. I could immediately tell that Serco maintained a structured and mission-driven environment. Even though I was an intern, I was treated as a valuable team member. I was given meaningful tasks and encouraged to participate in meetings and problem-solving discussions.
The company culture emphasized teamwork, accountability, and continuous learning.
While there was a strong focus on rules and compliance due to the nature of Serco’s clients, I never felt restricted. Instead, I felt supported, especially by my mentor and the other cybersecurity professionals on the team. The environment encouraged asking questions, trying out tools, and actively participating in projects. One of the things that stood out to me early on was how much emphasis Serco placed on documentation. Whether it was reporting a potential vulnerability or logging a task completion, every step needed to be properly recorded. This was new to me, but it helped me understand the importance of traceability and accountability in cybersecurity work, especially in an organization dealing with sensitive government data.
During my first two weeks, I was primarily shadowing senior engineers, attending training sessions, and learning how to use tools like Wireshark, Kali Linux, and Nessus within a secure virtual environment. I was also given reading assignments on topics like secure software development life cycles (SDLC), vulnerability management, and common attack vectors in enterprise systems. Even though my responsibilities started out small, I was surprised by how quickly I was included in real projects. By the end of the first month, I was already helping with network scans, assisting in identifying vulnerabilities in test systems, and preparing basic reports for my supervisor. This early experience gave me a solid understanding of Serco’s workflow and expectations, and it helped set the tone for the rest of the internship. I realized that the internship was not just about learning technical tools, it was about understanding how to work professionally in a secure, high-stakes environment.
Management Environment:
The management environment at Serco was both structured and supportive, which made it easier for me to adapt to the professional cybersecurity setting. Since Serco works with government agencies and handles sensitive data, the company follows a well-defined chain of command and operates within clearly outlined roles and responsibilities. This structure helped maintain accountability while also promoting team collaboration and communication. I was placed within a cybersecurity team that functioned as a sub-division of the broader Information Technology Services department. The team consisted of several full-time cybersecurity engineers, analysts, and compliance specialists, all of whom reported to a Cybersecurity Team Lead. The Team Lead, in turn, reported to a Cybersecurity Program Manager, who oversaw high-level planning, staffing, and policy enforcement across multiple projects.
As an intern, I reported directly to my assigned mentor, a senior Cybersecurity Engineer who has several years of experience working on federal cybersecurity contracts. My mentor served as my immediate supervisor and primary point of contact. He was responsible for assigning tasks, reviewing my work, answering my questions, and providing feedback. We held weekly one-on-one check-ins to review my progress and discuss learning goals, which I found incredibly helpful. One of the most impressive aspects of the management structure was its clarity. Everyone knew who to go to and for what. There were no mixed signals about roles or expectations, which made the work environment very efficient. At the same time, the culture was not overly rigid. The team lead encouraged open communication, and team members were willing to help each other out through different projects. Even though the work was serious and at high stakes, the environment felt welcoming and respectful.
The management style at Serco emphasized autonomy with accountability. After the first few weeks, I was trusted to handle certain tasks on my own, like conducting vulnerability scans and drafting technical documentation. However, I always had to log my work, submit it for review, and maintain clear documentation following company standards. This balance helped me develop both confidence and a sense of responsibility in my work. I also observed how the team used project management tools like Jira and Confluence to assign and track tasks, document progress, and maintain collaboration across teams. During daily stand-up meetings, each team member, including interns, had the opportunity to share what they were working on and raise any blockers they encountered. This level of transparency kept everyone informed and aligned.
Overall, the management environment at Serco fostered professional growth while also ensuring that all team members stayed focused, compliant, and goal-oriented. It gave me a realistic view of what it’s like to work in cybersecurity for a federal contractor and helped me develop soft skills like communication, teamwork, and accountability, which are just as important as technical knowledge in this field.
Work Duties:
Throughout my internship at Serco, I was assigned to various real-world tasks and projects that directly supported the cybersecurity operations team. These assignments allowed me to apply what I had learned in my courses at Old Dominion University while gaining valuable insight into how cybersecurity is implemented and maintained in an organization that serves federal government clients. I was heavily involved in internal processes, sandbox simulations, documentation, and compliance preparation activities.
My core responsibilities throughout the internship included:
- Conducting internal vulnerability assessments in test environments using Nessus and OpenVAS
- Reviewing and updating documentation for security incident response procedures
- Supporting the creation of user access control reviews
- Monitoring system logs and identifying possible anomalies for escalation
- Assisting with asset inventory updates to ensure systems were accurately reflected in compliance records
- Supporting the cybersecurity team in preparing for internal audits
These tasks helped reinforce critical habits of cybersecurity professionals: attention to detail, consistent documentation, proactive problem identification, and communication within a team. The systems I worked on were internal or sandbox environments used for demonstration, training, and simulation purposes, which gave me safe opportunities to practice without the risk of exposing sensitive federal systems. In addition to technical assignments, I was also tasked with creating and refining internal process guides based on the work I was doing. For instance, after completing a vulnerability assessment workflow, I was asked to document the entire process, from tool configuration to reporting standards, so that it could be used as a training resource for future interns or new team members. These documentation tasks sharpened my ability to write with clarity and precision, which is a critical skill in cybersecurity environments where every detail matters. I also contributed to drafting sections of the System Security Plan (SSP) under supervision, particularly in the areas related to access control and incident response. These documents are required for Authorization to Operate (ATO) under federal compliance frameworks and taught me a great deal about how organizations maintain accountability and transparency with their security posture.
Each of these tasks was directly tied to the company’s broader goal of maintaining operational security and preparing for both internal and external audits. For example, the vulnerability assessments I conducted helped identify configuration flaws in test systems, which could be addressed before rollout or audit review. Similarly, my assistance with access control logs helped the team verify that only authorized users had access to key resources. By contributing to these duties, I saw firsthand how even small tasks, like log analysis or policy review, are essential to the larger security ecosystem.
Application of Skills and Knowledge:
This internship allowed me to actively apply both the theoretical knowledge and technical skills I had gained during my time at Old Dominion University. Before the internship, I had already studied core cybersecurity concepts such as network defense, ethical hacking, encryption protocols, and compliance frameworks through coursework. I was comfortable using tools like Wireshark and basic Linux commands and had a solid understanding of risk assessment and cyber hygiene principles. However, being in the field showed me how these concepts are practiced under real-world conditions, especially in an environment that operates under strict federal guidelines.
One of the key technical areas where I applied and expanded my knowledge was vulnerability management. I had previously completed classroom labs using Nessus, but during the internship, I performed full scan configurations, analyzed results, and helped draft mitigation strategies with guidance from senior engineers. These real-world scenarios taught me how to interpret CVSS (Common Vulnerability Scoring System) scores more meaningfully, identify false positives, and prioritize vulnerabilities based on actual system risk and business impact.
I also deepened my knowledge of compliance and governance, particularly around NIST SP 800-53 and the Risk Management Framework (RMF). Through work on audit preparation and documentation review, I learned how these standards are implemented in federal systems—not just in theory, but through actual control testing, plan development, and continuous monitoring. This experience strengthened my understanding of how cybersecurity goes beyond technical defenses to include policy creation, risk evaluation, and procedural compliance.
Additionally, my soft skills were put to use and improved throughout the internship. Writing documentation, presenting findings during meetings, and collaborating with team members required me to communicate clearly and professionally. I became more confident when interacting with senior staff and improved my ability to ask meaningful questions, propose ideas, and accept constructive feedback. By combining technical execution with professional communication, I learned how cybersecurity roles operate in cross-functional teams and support an organization’s mission from behind the scenes.
Academic Preparation and Skill Alignment:
The cybersecurity curriculum at Old Dominion University gave me a strong foundation that helped me transition smoothly into my internship at Serco. Courses such as Fundamentals of Cybersecurity, Network Security, Risk Analysis, and Cyber Law and Ethics introduced me to essential topics and tools that I later encountered on the job. My previous experience with virtual labs, packet sniffing exercises, and security simulations prepared me to approach tasks like vulnerability scanning, log analysis, and secure configurations with confidence. The theoretical grounding I received through my classes allowed me to understand not only what to do in cybersecurity but why each task was important.
One specific example of this alignment was my familiarity with the Risk Management Framework (RMF). In my coursework, I studied NIST standards and the steps of RMF in detail. During my internship, I was able to connect that theoretical understanding to actual RMF documentation and processes in a federal environment. Seeing how each control was implemented and validated, whether through audit logs, access controls, or encryption protocols, gave me practical insight into compliance enforcement and system accreditation.
In addition, the writing and documentation skills emphasized in my classes were extremely relevant at Serco. Technical communication is a key part of cybersecurity work, especially when documenting incidents, drafting reports, or contributing to system security plans. Assignments and group projects at ODU trained me to write clearly and logically, a skill I used regularly during the internship to document procedures, findings, and technical analysis for my team. I also noticed that having experience in collaborative academic settings helped me work more effectively with my internship team. Whether I was participating in stand-up meetings or reviewing reports with my mentor, I was comfortable contributing to discussions, asking questions, and explaining my reasoning.
However, there were also a few areas where the internship introduced concepts I had not yet encountered in school. For example, I had not previously worked with tools like eMASS (Enterprise Mission Assurance Support Service) or STIGs (Security Technical Implementation Guides), both of which are crucial in federal compliance settings. While I understood the general idea of system hardening and compliance testing, learning how these tools functioned in practice added a new layer to my education. These gaps were not a weakness of the curriculum, but rather a reminder that the field is vast and constantly evolving. Encountering new technologies and standards during the internship motivated me to explore them further outside of work hours and consider taking advanced electives or certifications after graduation.
Overall, my academic experience provided a solid framework that prepared me well for my internship responsibilities. The connection between classroom learning and real-world application became increasingly clear as I worked through projects and contributed to the cybersecurity team. The hands-on experience at Serco did not just reinforce what I had learned at ODU, it expanded it in ways that textbooks and simulations could not fully replicate.
Evaluation of Learning Objectives:
At the outset of my internship at Serco, I outlined three specific learning objectives that I hoped to accomplish: (1) apply encryption and secure communication techniques in real-world cybersecurity environments, (2) gain hands-on experience in risk management and incident response procedures within an organization that supports federal agencies, and (3) improve my professional communication and collaboration skills within a structured cybersecurity team. As I reflect on the past few months, I am confident that each of these objectives was not only met but exceeded in ways that enriched both my technical competence and professional growth.
The first objective, applying encryption and secure communication techniques, was fulfilled through my exposure to various tools and procedures Serco uses to ensure data security across their operations. While I didn’t directly configure encryption protocols, I participated in reviewing existing security controls during internal audits and compliance preparation. I worked with secure remote access tools that utilized TLS (Transport Layer Security) and multi-factor authentication (MFA) to protect sensitive systems. I assisted in documenting encrypted communication flows between internal systems and third-party services, and I analyzed system settings to verify the correct implementation of encryption policies. This hands-on exposure gave me practical insight into the role encryption plays in protecting both data-in-transit and data-at-rest, and how these technical controls align with federal cybersecurity standards such as FIPS 140-2 and NIST SP 800-53.
The second objective, gaining real-world experience with risk management and incident response, was a core component of my internship. One of my main responsibilities involved conducting internal vulnerability scans using tools like Nessus and OpenVAS, followed by reviewing scan reports, identifying high-risk vulnerabilities, and working with senior engineers to draft mitigation steps. I learned how to interpret CVSS scores and contextualize the risks based on asset criticality and potential business impact.
Additionally, I was introduced to the components of an incident response lifecycle and observed how the team used simulation exercises to practice their readiness. I reviewed incident response playbooks and learned how real-world scenarios like phishing, brute-force attempts, and unauthorized access attempts were detected and escalated. Although I wasn’t responsible for managing any live incidents, being involved in mock response drills and documentation updates provided me with firsthand knowledge of how cybersecurity teams prepare for and respond to threats in a fast-paced environment. It was fascinating to see how response efforts were coordinated among team members and aligned with documented policies and compliance requirements.
The third objective, enhancing my professional communication and collaboration skills, was perhaps the most transformative part of the internship. Coming from an academic background, I had limited experience in contributing to team-based projects outside of school. At Serco, I was immersed in a collaborative work culture where I had to regularly participate in stand-up meetings, provide status updates, take part in collaborative documentation tasks, and communicate with both technical and non-technical stakeholders. Initially, I was nervous about speaking up during meetings, but with encouragement from my mentor and peers, I gradually became more confident. I learned how to ask clarifying questions, summarize technical findings in clear and concise language, and tailor my communication depending on the audience.
One example that stands out was when I was asked to present my findings from a vulnerability assessment to the team. I created a slide deck, walked the team through my process, explained key vulnerabilities and their implications, and discussed potential mitigation strategies. Although it was a relatively informal presentation, it marked a milestone in my confidence as a cybersecurity communicator. The positive feedback I received encouraged me to continue improving my ability to translate complex technical topics into accessible explanations, a vital skill for cybersecurity professionals who often work across departments and with leadership teams.
Ultimately, my internship experience at Serco fulfilled each of my learning objectives while offering me opportunities to grow beyond what I had anticipated. I developed technical competencies in key cybersecurity practices, gained exposure to industry-standard tools and compliance frameworks, and significantly improved my interpersonal and communication skills in a professional context. These experiences not only reinforced the importance of setting clear goals but also demonstrated how hands-on work can accelerate both academic and personal development. This evaluation also affirmed that cybersecurity is not just about technical expertise, but about being an adaptable, accountable, and collaborative team member who contributes to the broader mission of organizational security.
Most Motivating/Exciting Aspects:
One of the most motivating aspects of my internship at Serco was the opportunity to contribute to real projects that had a clear purpose and impact. Even as an intern, I was trusted with responsibilities that mattered, like conducting vulnerability scans, documenting security findings, and assisting with compliance-related tasks. Knowing that the work I was doing helped support systems used by federal agencies gave me a strong sense of purpose. It wasn’t just about completing assignments; it was about being part of a team working to protect national infrastructure. That level of responsibility pushed me to stay focused, ask questions, and constantly look for ways to improve.
Another thing that motivated me was the learning environment. My mentor and the rest of the cybersecurity team were incredibly supportive and generous with their time and knowledge. Whenever I had questions, they explained things clearly and connected them to bigger concepts. They made sure I understood why something mattered, not just how to do it. Their guidance made me feel valued and encouraged me to challenge myself. I also appreciated that they gave me space to learn by doing, allowing me to take the lead on small tasks and follow through with them from start to finish.
The variety of experiences I was exposed to also kept me motivated. Each week, I was learning something new, whether it was a new tool like eMASS or STIG Viewer, or a new policy I needed to understand for compliance documentation. I never felt like I was stuck doing the same repetitive work. Instead, I was gradually introduced to more complex tasks that helped me grow both technically and professionally. That steady increase in responsibility and trust was a big confidence booster and made me excited to come to work each day.
Finally, being part of a professional, mission-driven workplace like Serco itself was very inspiring. The structured yet flexible work culture, the professionalism of the team, and the emphasis on continuous learning made me look forward to a future career in cybersecurity. It was motivating to be surrounded by people who took their work seriously and cared about making a difference through technology. This environment showed me what it looks like to work at a high standard, and it made me want to match that level of commitment in everything I did.
Most Discouraging Aspects:
While my internship at Serco was overall a very positive and enriching experience, there were a few moments that I found discouraging, mainly because of how different the real-world work environment can be from the academic one. One of the first challenges I faced was adjusting to the pace of cybersecurity work in a government contracting setting. At times, the workflow would be extremely slow due to long approval processes, restricted access to certain tools, or delays in task assignments that were outside of the team’s control. For someone eager to learn and stay engaged, it was difficult at first to deal with downtime or waiting on permissions, especially in the early stages of the internship when I was still getting cleared for access to specific systems.
Another discouraging aspect was realizing how steep the learning curve could be. Although I had a strong academic background, I quickly noticed there were many tools, platforms, and acronyms used daily that I wasn’t familiar with. For example, tools like eMASS, STIG Viewer, and even documentation formats for compliance reports were completely new to me. During my first few weeks, I often felt overwhelmed by how much I didn’t know. There were times I questioned whether I was ready or capable enough to work in a professional cybersecurity environment. Even though my team was supportive, it was tough to accept that I couldn’t immediately master everything. In addition, the level of formality and attention to detail required in documentation sometimes felt overwhelming. Every task, no matter how small, had to be logged, reviewed, and written in a specific format to meet government compliance standards. I understood the importance of accuracy and traceability, but it was still discouraging at times to have my work sent back for revisions, especially when I had already spent a lot of time on it. It was a humbling reminder that cybersecurity isn’t just about finding vulnerabilities or using technical tools, it’s also about clear communication, precision, and following established processes without shortcuts.
Despite these discouraging moments, I now realize they were important learning experiences. They taught me patience, resilience, and the importance of asking for help when I needed it. Over time, I became more comfortable with the slower pace of government cybersecurity work and learned how to make the most of downtime by reviewing documentation, exploring training resources, or shadowing a teammate. I also became more confident in dealing with unfamiliar tools and learned to see mistakes or revisions as part of the learning process. While these challenges were frustrating at times, they ultimately made me stronger and more realistic about what a career in cybersecurity truly involves.
Most Challenging Aspects:
While there were many rewarding aspects of my internship, there were also a few unique challenges that pushed me outside of my comfort zone in ways I hadn’t expected. One of the most difficult parts of the experience was learning how to interpret and apply government cybersecurity policies in practical, day-to-day tasks. It’s one thing to read about frameworks like NIST 800-53 or FISMA in a classroom setting, but it’s another thing entirely to translate those broad policies into specific security actions for a system. Another challenge I faced was related to working with large sets of technical documentation. In school, most of our assignments and lab reports are relatively short and targeted. At Serco, I often had to read through lengthy system security plans, audit preparation materials, or compliance checklists that could be dozens, sometimes hundreds, of pages long. Keeping track of details across multiple documents, cross-referencing them, and ensuring consistency was overwhelming at first. I had to develop new habits like using annotation tools, maintaining document summaries, and organizing my notes more effectively. Working with multiple teams across different time zones also proved to be more challenging than I expected. Some of the cybersecurity specialists or engineers I needed input from were located in other states or even overseas, depending on the project. Coordinating schedules, getting timely responses, or trying to resolve issues without being able to meet face-to-face sometimes made collaboration slower and more complicated. I had to learn how to be patient while still being persistent, and how to communicate clearly in emails and written messages to avoid confusion. These challenges were difficult in the moment, but looking back, I’m grateful for them. They helped me grow more than I expected, pushing me to think critically, stay organized, manage uncertainty, and trust myself in a professional setting. I now feel more prepared to face similar situations in the future, both during my remaining time at Old Dominion University and in my future cybersecurity career.
Recommendations for Future Interns:
For future interns at Serco or similar cybersecurity roles, I recommend going in with a willingness to learn and ask questions early and often. Don’t be afraid to admit what you don’t know, your team understands you’re there to learn. Take detailed notes, especially during onboarding and training sessions, as they will be useful later. Familiarize yourself with government cybersecurity standards like NIST and RMF before the internship starts; it will help you understand your tasks faster. Also, stay organized by using to-do lists or project tracking tools, especially when juggling multiple responsibilities. Finally, take the initiative; volunteer for tasks, ask to shadow others, and show your interest in learning more. The more effort you put in, the more rewarding the experience will be.
Conclusion:
Overall, my internship at Serco was a valuable and transformative experience that gave me a clear picture of what it means to work in the cybersecurity field. I gained practical, hands-on experience with industry tools, government compliance standards, and professional workflows that went far beyond what I had encountered in the classroom. I developed both technical skills, like vulnerability scanning, secure documentation, and policy review, and soft skills, like communication, time management, and teamwork. Most importantly, I learned how to adapt in a professional environment, handle unfamiliar challenges, and contribute meaningfully to a mission-driven organization. This experience will influence the rest of my time at Old Dominion University. I now have a better understanding of which areas I want to focus on in my studies, such as risk management and security operations. It also gave me the motivation to pursue certifications like Security+ or CISSP to strengthen my credentials. Looking ahead, this internship helped shape my professional goals. The skills, experiences, and connections I gained at Serco will serve as a strong foundation for launching my career. I now feel more prepared, more focused, and inspired to continue building my future in this field.
Appendices/Work Samples
The following work samples represent tasks and projects I contributed to during my internship at Serco. Due to the sensitive nature of some internal documents, the samples below have been modified or summarized to maintain confidentiality while still demonstrating the type of work completed.
Appendix A: Vulnerability Scan Report Summary
This document summarizes the results of an internal vulnerability scan I conducted using Nessus on a test environment. It includes identified vulnerabilities, severity ratings based on CVSS scores, recommended mitigation strategies, and notes on false positives. I worked under supervision to complete this scan and drafted the report as part of my weekly documentation responsibilities.
Tool Used: Nessus
Scan Target: Internal Test Environment (192.168.10.0/24)
Key Findings:
– CVE-2023-12345: Apache HTTP Server Buffer Overflow (CVSS 8.1) – Requires immediate patching.
– CVE-2022-56789: OpenSSL Information Disclosure (CVSS 7.4) – Recommended configuration update.
Action Taken:
– Created mitigation ticket in Jira for Apache patch rollout.
– Submitted summary to supervisor for review and escalation.
Appendix B: System Security Plan (SSP) – Access Control Section Draft
This sample includes a portion of the System Security Plan I contributed to, specifically the section related to Access Control (AC) family controls under NIST SP 800-53. I helped review and update this section based on actual system configurations, ensuring that it met compliance requirements and was ready for internal review.
Control Family: Access Control (AC)
Control: AC-2 – Account Management
Implementation Statement:
The system implements role-based access control (RBAC). User accounts are provisioned by the system administrator following a documented approval workflow. Access reviews are conducted quarterly. Account activity is logged and reviewed weekly.
Appendix C: Security Incident Response Process Guide
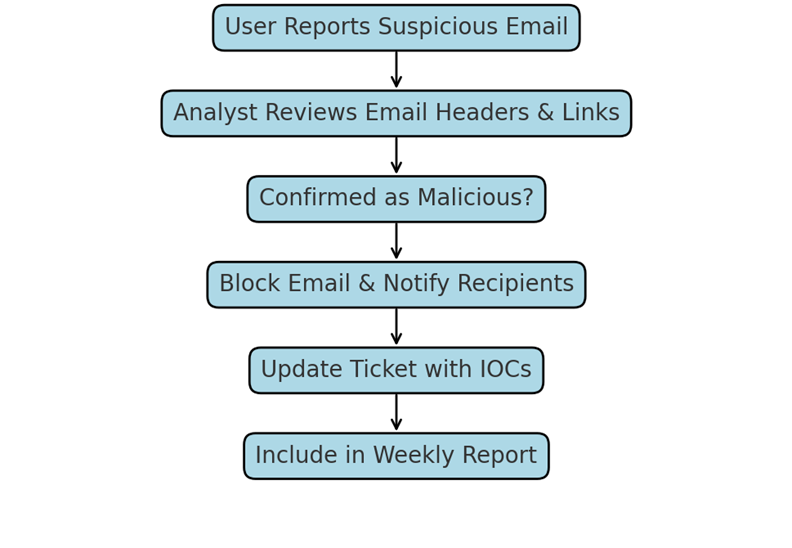
As part of my documentation assignments, I helped revise the internal guide used to respond to common cybersecurity incidents such as phishing and unauthorized access attempts. This sample includes an excerpt from the revised procedure, along with flowcharts for incident escalation and response steps.
Incident Response Flow (Phishing Email):
1. User reports a suspicious email via Outlook plug-in.
2. Analyst checks email header and links using sandbox analysis.
3. If confirmed malicious, the email is blocked, and all recipients are notified.
4. Incident ticket is updated with IOCs and remediation steps.
5. Weekly reports include an incident summary and lessons learned.
Appendix D: Daily Task Tracker
This is a simplified version of the task tracker I maintained throughout my internship. It includes tasks completed, tools used, and notes on outcomes or follow-up actions. Keeping this tracker helped me stay organized and reflect on my progress during weekly meetings with my mentor.
| Date | Task | Tool Used | Outcome / Notes |
| 02/21/2025 | Internal Vulnerability Scan | Nessus | Found 2 high, 3 medium vulnerabilities |
| 03/14/2025 | Updated Access Control Docs | Word, Confluence | Reviewed by mentor |
| 03/23/2025 | Audit Prep – Checklist Review | Excel | Flagged 1 missing item for follow-up |