Journal Entry #1
After reviewing the NICE framework’s work role categories, I find myself most interested in the investigative side of cybersecurity. This path blends critical thinking, technical expertise, and real-world impact. Roles such as cybercrime investigator or digital forensics analyst appeal to me because they involve analyzing incidents, uncovering evidence, and preventing future attacks. I enjoy the challenge of piecing together digital findings to understand how breaches occur.
On the other hand, areas like implementation and operation are less appealing. Although they are essential for maintaining secure systems, the routine nature of system administration does not provide the same complexity or excitement. I am drawn to dynamic environments where I can solve problems and contribute to justice through technology.
Journal Entry #2
Empiricism makes cybersecurity stronger by focusing on real evidence instead of guesswork. Collecting data like network traffic, user activity, and attack patterns helps security teams spot new threats as they appear. It also shows whether current defenses are actually working or if adjustments are needed. By studying this data over time, organizations can stay ahead of attackers and develop smarter strategies that evolve with changing risks. Empirical analysis also improves planning by making incident response and threat prediction more accurate. In short, relying on observed evidence keeps cybersecurity practical, adaptable, and better prepared for real-world challenges
Journal Entry #3
Researchers gain a better understanding of patterns and trends in the data breaches by using the Privacy Rights Clearinghouse’s publicly available data. The database contains comprehensive details pertaining to thousands of breaches that have been disclosed since 2005, including the kind of breach, the businesses impacted, the data exposed, and the method in which it was discovered. Researchers can determine which industries are most at risk, what kinds of attacks are growing more frequent, and how the scope of breaches has evolved over time by examining this data. This information can be used to predict future patterns in breaches and to help companies and legislators create more robust safeguards and efficient preventative measures. Furthermore, comparing data from different states might indicate areas where privacy las could be strengthened and show variations in reporting procedures.
Journal Entry #4
My digital encounters have a strong connection to Maslow’s Hierarchy of Needs. For starters, having access to gadgets and the internet is necessary for my daily life and academic work, especially as a cyber security student. I use cybersecurity solutions like VPNs and multi-factor authentication to safeguard my data. Online communities provide a sense of belonging; I feel linked through my tech communities, group chats, and class forums. Building my e-portfolio and obtaining certifications like CompTIA Security+, which increase confidence and recognition, are examples of how I demonstrate my sense of self-worth. Finally, utilizing technology to work toward my long-term objective of becoming a cybersecurity project manager supports self-actualization. I can study, lead, and develop using digital tools in ways that support my personal and professional goals.
Journal Entry #5
Among the eight motives for cybercrime, financial gain ranks highest because it’s the most practical and widely understood. Hackers often target systems to steal money, cryptocurrency, or data they can sell, as seen in the BitMart hack and HP’s infographic on cybercriminal spending. Political motives come next, with hacktivist groups launching attacks to protest governments or influence public opinion. Recognition ranks third because some hackers seek fame or validation, even from institutions like NASA. Curiosity, especially among youth, is a strong fourth, as shown by the 15-year-old who hacked NASA just to explore. Revenge is fifth, driven by personal emotions like anger or betrayal. Sixth is the “multiple reasons” category, which reflects the complex mix of ego, money, and ideology behind many attacks. Entertainment ranks seventh, as thrill-seeking lacks deeper purpose. Boredom ranks last because it’s the least compelling motive, often linked to impulsive or harmful behavior without clear intent.
Journal Entry #6
Fake websites are a growing threat in the digital world, often designed to mimic legitimate platforms while tricking users into sharing personal or financial information. According to Kaspersky, scam websites typically use emotional manipulation, urgent messaging, and deceptive design to lure victims. For example, “US-GovLottery.com” falsely claims to be a government-run lottery, while demanding upfront fees, unlike the real Powerball.com, which never asks winners to pay to claim prizes. Similarly, “PayPal-Verify.net” mimics PayPal’s branding but uses a suspicious domain and pressures users to update payment info, a classic phishing tactic. In contrast, PayPal.com uses secure login protocols and never sends unsolicited requests for sensitive data. Another fake site, “FreeCryptoBonus.io,” promises free cryptocurrency with no verifiable company background, unlike Coinbase.com, which provides transparent compliance and security measures. Norton highlights spoofing techniques like domain manipulation (e.g., “amaz0n” instead of “amazon”) to trick users into clicking malicious links. The FTC warns that scammers often exploit trending topics or emergencies to create urgency and bypass skepticism. Recognizing these red flags, such as poor grammar, suspicious URLs, and unrealistic offers, is essential for staying safe online.
Journal Entry #7

Sample Example: (image #17) Man on his laptop in a coffee shop.
Meme: “When the Wi-Fi is free, the coffee is addicting, and you forget public networks are hacker playgrounds”
Explanation related to Human-centered cybersecurity: This highlights how users often prioritize comfort, aesthetics, and convenience over digital safety. The casual, inviting environment encourages relaxed behavior, making individuals more likely to connect to unsecure public Wi-Fi without considering the risks of man-in-the-middle attacks. Human-centered cybersecurity emphasizes designing systems and nudges that account for these behavioral tendencies.
Journal Entry #8
After watching the video, it’s clear that movies and television often misrepresent cybersecurity and hacking. Many scenes show hackers breaking into systems instantly with dramatic visuals and unrealistic speeds. Cybersecurity calls for a great deal of meticulous preparation, technical expertise, and frequent cross-team cooperation. Portrayals found in media can lead to misunderstandings about what cybersecurity professionals do. Instead of chaos and crime, the field focuses on protecting data, managing risks, and following ethical guidelines. Public perception is influenced by the media, and false portrayals of cybersecurity can have an impact on how people perceive the field and its significance. Recognizing the difference between entertainment and real-world cybersecurity helps build a more informed understanding of challenges and responsibilities in the field.
Journal Entry #9
Based on my responses, I scored a 0, which suggests my social media use falls within a typical or non-problematic range. I found the scale to be thoughtfully constructed as it doesn’t just measure time spent online but instead focuses on behaviors that might signal deeper issues, like withdrawal, deception, or displacement. That emphasis on emotional and social impact makes the assessment feel more relevant and insightful. It’s also worth noting that social media habits vary widely across cultures. Factors like access to technology, societal norms, and the role of digital platforms in daily life all shape how people engage online. In some places, social media is a vital outlet for connection and self-expression; in others, it might be more restricted or play a smaller role. Recognizing these differences helps us interpret usage patterns more accurately and avoid making broad assumptions about what “normal” digital behavior looks like.
Journal Entry #10
https://www.sciencedirect.com/science/article/pii/S2451958825000831
The article “A Survey of Social Cybersecurity: Techniques for Attack Detection, Evaluations, Challenges, and Future Prospects” discusses how cybersecurity is no longer just about the protection of computers but is also about the protection of user privacy and security amongst individuals and communities. It explores issues such as misinformation, social engineering, and the spread of false narratives that can ultimately harm public trust. What caught my attention was how researchers are combining technology and social science to better understand these problems. The article also makes note of challenges such as the lack of trustworthy data and the constant advancement of online threats. Overall, it made me understand that cybersecurity today is deeply connected to human behavior and emphasizing the need to maintain integrity in our digital world.
Journal Entry #11
Nicole Enesse’s YouTube video on cybersecurity analyst careers shows how social skills are just as important as technical prowess. One major theme is teamwork; analysts need to work closely with others to identify threats and respond quickly, which takes strong communication and trust. She also highlights the ethical aspect of the job, since analysts handle sensitive data and face tough decisions that require integrity. Another key point is the ability to explain technical risks in a way that everyone can understand and be able to mitigate/eliminate them. Collaboration, ethics, and communication aren’t just soft skills; they are essential ingredients of effective cybersecurity practice.
Journal Entry #12
“SAMPLE DATA BREACH NOTIFICATION”https://dojmt.gov/wp-content/uploads/Glasswasherparts.com_.pdfLinks to an external site.
From an economic standpoint, a cost-benefit analysis is evident: the company delayed customer notification due to law enforcement requests, likely weighing the cost of early disclosure against the potential investigative outcomes and reputational damage. Agency theory also applies; the breach occurred through a third-party platform provider, illustrating risks when delegating responsibilities to external agents whose incentives may not align with the company’s.
Psychologically, prospect theory helps explain customer reactions: individuals perceive the potential loss of financial data more intensely than the abstract benefit of security measures. Trust theory is also relevant; the letter attempts to rebuild consumer trust by offering security and transparency, recognizing that trust is fragile and essential for continued business. Together, these theories underscore how economic decisions and psychological responses converge in breach management.
Journal Entry #13
https://doi.org/10.1093/cybsec/tyab007
Summary: Bug bounty programs show how cybersecurity is shaped just as much by people as by technology. The article’s literature review explains that ethical hackers are not only motivated by money but also by curiosity, challenge, and the chance to build a reputation. Organizations adopt these programs based on their culture and their comfort with risk. The findings were especially interesting because raising bounty amounts does not greatly increase participation, and large well known companies do not necessarily attract more reports. This means smaller organizations can benefit just as much. Overall, bug bounty policies work because they rely on a mix of incentives, community values, and organizational behavior rather than technical skill alone.
Journal Entry #14
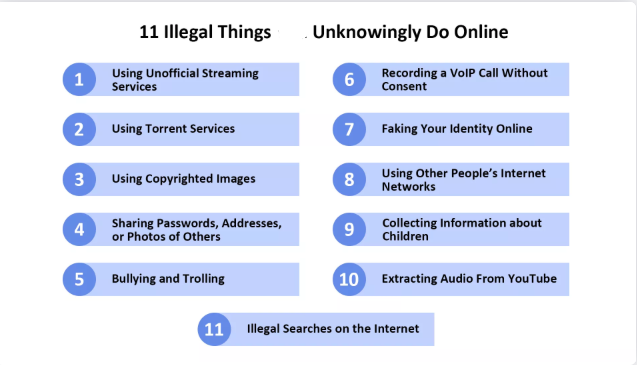
Andriy Links to an external site.Slynchuk
After reviewing Andriy Slynchuk’s article, I believe the five most serious online violations are identity theft, cyberbullying, accessing child pornography, hacking and illegally downloading copyrighted content. These aren’t just technical issues; they cause real harm. Identity theft can destroy someone’s finances and reputation. Cyberbullying leaves lasting emotional scars, especially on young generations. Child pornography is a horrific crime in itself, perpetuating abuse. Hacking can leak sensitive data, leave systems inoperable, shut down hospitals’, putting lives at risk. Although illegal downloading seems harmless, it undermines the work of genuine creators and can lead to legal issues. These actions cross ethical lines and often result in punishable consequences
Journal Entry #15
The video raises important ethical questions about how artificial intelligence and deepfakes can be misused to exploit people. It highlights concerns about privacy, consent, and the difficulty of distinguishing truth from deception in a digital world. For me, the biggest issue is accountability. Who should be held responsible when AI tools are used for fraud or manipulation? Society needs to address these concerns through stronger regulations, public education, and technological safeguards. Teaching digital literacy can help individuals recognize scams, while laws and detection systems can limit misuse. Ultimately, the ethical challenge is balancing innovation with protection, ensuring AI benefits society without becoming a weapon for exploitation.