Cybersecurity Risk Analysis
Cybersecurity risk analysis involves identifying vulnerabilities, evaluating threats, and understanding the potential impact of security incidents on organizations. Through coursework and assignments, I developed the ability to analyze cybersecurity risks and understand how organizations prioritize security decisions.
Artifact 1 : Information Security Policy & HIPAA Compliance Discussion
Description: This discussion examined the importance of information security policies and regulatory compliance in protecting sensitive healthcare data. In my response, I analyzed the role of HIPAA regulations and the CIA triad confidentiality, integrity, and availability in guiding cybersecurity practices. I also referenced the Anthem healthcare data breach as a real-world example of how insufficient security controls can lead to major financial and legal consequences.
Excerpt from Coursework
When it comes to creating and enforcing an information security policy for a company in this country, one of the most significant compliance laws that needs to be accounted for is HIPAA, the Health Insurance Portability and Accountability Act, which is quintessentially just following a concept that is widely known in the cybersecurity realm. At least, it’s something I learned very early on in my journey in this field: the CIA triad of confidentiality, integrity, and availability. Regarding HIPAA, this pertains to information in the healthcare sector. Since this is a law, organizations are mandated to implement security procedures that assess components such as employee training, incident response, and access controls. While in other industries following these procedures may be optional, that is not the healthcare case; if they are ignored, it can result in serious legal trouble for the institution and substantial financial consequences. A real-world example of the impact HIPAA has is the Anthem data breach, which occurred in 2015. Anthem is one of the largest healthcare providers in the United States, and, unfortunately, it was the victim of a cyberattack that exposed sensitive information belonging to nearly 8 million patients. Due to the large-scale nature of this case, the U.S. Department of Health and Human Services Office for Civil Rights investigated the incident, which resulted in Anthem paying a $16 million settlement for failing to have proper protocols in place to safeguard this incredibly sensitive data regarding their clients’ healthcare.
Artifact 2: Risk Management Planning (POA&M Discussion)
Description: This discussion examined how organizations manage cybersecurity risks using structured planning frameworks. In my response, I analyzed the role of a Plan of Action and Milestones (POA&M) and how it is used within the NIST cybersecurity framework to track vulnerabilities, assign responsibility for mitigation, and ensure security improvements are implemented over time.
Excerpt from Coursework
A Plan of Action and Milestones (POA&M) is an effective tool for managing the ongoing risks an organization may face. Since, instead of ignoring the problem and hoping for the best, an actual plan is put in place with trackable goals to ensure progress is being made. To truly see the beauty of (POA&M) in action, a good place to look is the National Institute of Standards and Technology (NIST). Within this framework, a potential vulnerability is noted, and a resolution is decided upon. It is then assigned to the responsible party, who is given deadlines for completing certain activities. This guarantees that a solution is on the way, rather than leaving an organization exposed to potential cyberattacks because nothing was done.A POA&M will help decision makers within an organization determine what needs to be addressed first, based on which risk would have the greatest impact if exploited. Having a clearer understanding of what’s actually going on will lead to better resource allocation to solve problems. The aspects of POA&M that make it such an effective tool are how it makes everything simple by answering the who,what,where,why, and how of the isese so everyone is on the same page and knows what needs to be done. As long as it is followed properly and systems are regularly updated, POA&M can be a powerful tool for long-term risk reduction planning.
Artifact 3: Quantitative vs. Qualitative Risk Assessment Discussion
Description: This discussion explored the differences between quantitative and qualitative risk assessment methods used in cybersecurity risk management. In my response, I analyzed how organizations measure risk using concepts such as Single Loss Expectancy (SLE) and Annual Rate of Occurrence (ARO). This assignment helped me better understand how organizations evaluate financial risk and determine appropriate security measures based on potential threats.
There are some key differences between quantitative and qualitative risk assessments, primarily in the manner in which they measure the level of risk and then communicate it outward. Quantitative risk assessment is primarily focused on the numbers and the associated financial cost of a potential loss. There are various ways to calculate the amount that could be lost, including Single Loss Expectancy (SLE) and Annual Rate of Occurrence (ARO). This method is valid and has its place, particularly for larger organizations that are well-established and have data they can look back on to make these informed decisions. An example of this could be a large healthcare facility that looks at the data and calculates that a potential ransomware attack could cost them a couple of million dollars, and then uses that data to make a decision on what appropriate measures they should take to minimize the amount of damage as much as possible. Now, qualitative is not specific; it takes into account the likelihood of an incident occurring and the potential impact it could have. It’s substantially more flexible and more applicable to an organization that is not as well established and can view the details from previously acquired data to make informed decisions. An example of this could be a small startup that feels like they are at a high likelihood of experiencing a phishing attack based on data from within its industry.
Network Security & Infrastructure
Network security focuses on protecting systems, understanding how devices communicate across networks, and analyzing the infrastructure that supports modern digital communication. Through coursework and hands-on labs, I developed foundational knowledge of networking concepts such as the OSI model, network topologies, and the devices responsible for directing network traffic. These assignments helped strengthen my understanding of how networks operate and how cybersecurity professionals analyze network environments when identifying potential vulnerabilities or security threats.
Artifact 1: OSI Model Networking Lab (CompTIA Network+)
Description: This lab introduced the Open Systems Interconnection (OSI) model, which explains how data moves through different layers of a network. The assignment helped me understand how communication between devices occurs across networks and how each layer contributes to the overall networking process. Understanding the OSI model is important for cybersecurity professionals because it provides a framework for identifying where network issues or potential security threats may occur.
Screenshot of lab report
Artifact 2: Networking Topologies and Characteristics Lab (CompTIA Network+)
Description: This assignment explored different network topologies and their impact on communication and performance within a network environment. Through this lab, I learned how network structures such as star, bus, and mesh topologies influence reliability, efficiency, and security within an organization’s infrastructure.
Screenshot of lab report
Artifact 3: Networking Devices Identification Lab Discussion
Description: This lab focused on identifying common networking devices such as routers and hubs and understanding how they manage network traffic. Completing this assignment strengthened my understanding of how network infrastructure components function and how they support communication within a network.
Screenshot of coursework
Professional Communication & Leadership
Professional communication and leadership are essential skills in both academic and professional environments. Through my leadership roles and organizational responsibilities, I developed experience in planning events, coordinating tasks, and communicating expectations clearly with teams. These experiences strengthened my ability to organize projects, collaborate with others, and manage responsibilities in a structured and professional manner.
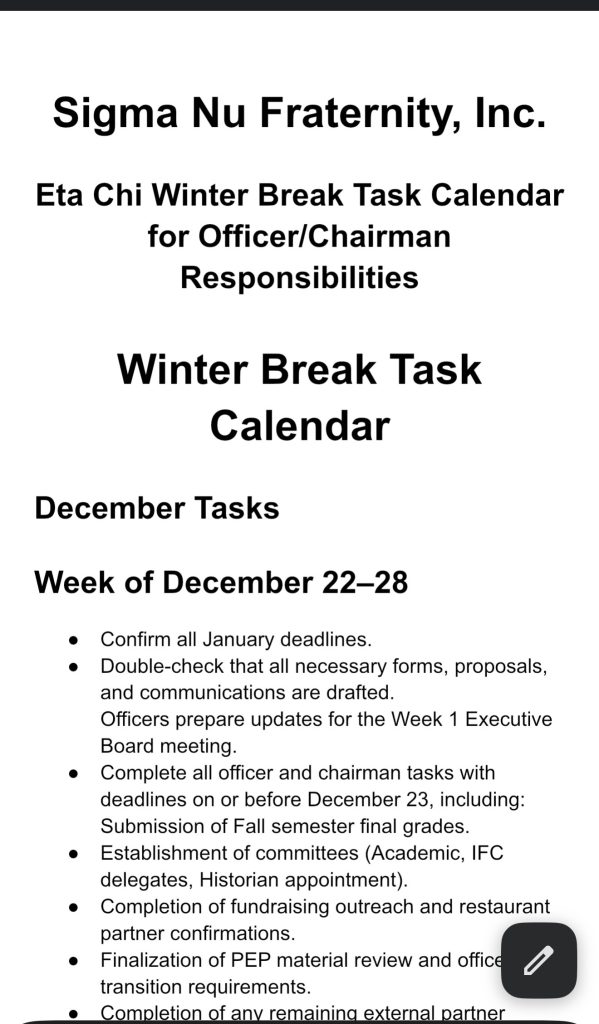
Artifact 1: Winter Break Leadership Task Calendar
Description: This artifact is a leadership task calendar that I created for the officers and chairmen of Sigma Nu to organize responsibilities during winter break. The calendar outlined important tasks, deadlines, and expectations to ensure that preparations for the upcoming semester were completed on time. Creating this document required organization, planning, and clear communication with leadership members.
Screenshot of the Sigma Nu Eta Chi Winter Break Task Calendar for Officer/Chairman Responsibilities.
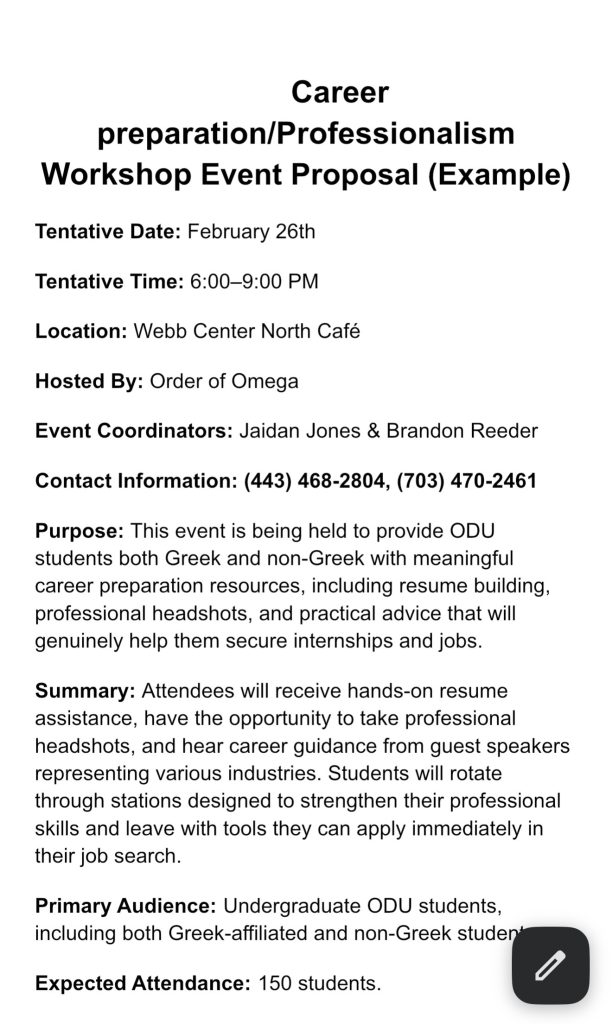
Artifact 2: Career Preparation & Professionalism Workshop Event Proposal
This artifact is an event proposal created for a Career Preparation and Professionalism Workshop organized through Order of Omega. The proposal outlines the event’s purpose, schedule, location, and intended outcomes. Planning this event required coordination, organization, and professional communication with multiple individuals to ensure the event could provide meaningful career preparation resources for students.
Screenshot of the Career Preparation and Professionalism Workshop Event Proposal.
Artifact 3: Fall 2025 Event Planning Schedule
This artifact is a schedule of events created for the Fall 2025 semester to organize chapter activities and important dates. The document helped ensure that members were informed about upcoming events, deadlines, and responsibilities. Creating and distributing this schedule required planning, organization, and clear communication to ensure that all members understood the semester’s schedule.
Screenshot of the Fall 2025 Schedule of Events and Important Information.