This is one of the first courses, that I have taken in my Cybersecurity Masters graduate studies. This course provides me a overview of the field of cybersecurity covering many essential cybersecurity principles. This includes Cybersecurity principles that evolve around, computer systems architectures, critical infrastructure, cyber threats and vulnerabilities, cryptography, cryptographic protocol design, information assurance, network security, and risk assessment and management. This course further allows a student to formalize themselves with the importance the cybersecurity field holds within the digital realm, and develop a foundation for further studies.
Artifact1
Reflection essay:
This reflection assignment allowed me to display the importance of how this course has prepared me both academically and personally for my future goals, and develop a specific insight gained during class. When it comes to the way in which the course prepared academically, it allowed me to understand core cybersecurity topics in depth, through various hands on labs, readings, and discussions, which overall strengthened my understanding of various cybersecurity concepts. The way in which this course strengthened my professional goals is that it allowed me to gain expierence using a variety of tools, in which I will look to use within my goal of being a cybersecurity analyst. The insight in which I further looked to discuss, was the importance of knowing encryption concepts, and the devices and software they are involved with such as File level encryption and hardware security module.
Artifact 2
Discussion board:
This discussion board allowed me to develop critical thinking skills, when it came to the topic of, understanding the importance of if program and application developers should be required to provide security updates for a period of time for the products they develop. My answer was yes, due to the fact in which most programs and applications look to provide security updates for there customers to help protect them from known cyber threats and various vulnerabilities that can be exploited by attackers, if not already patched, and ensure trust within custumers.
Artifact 3
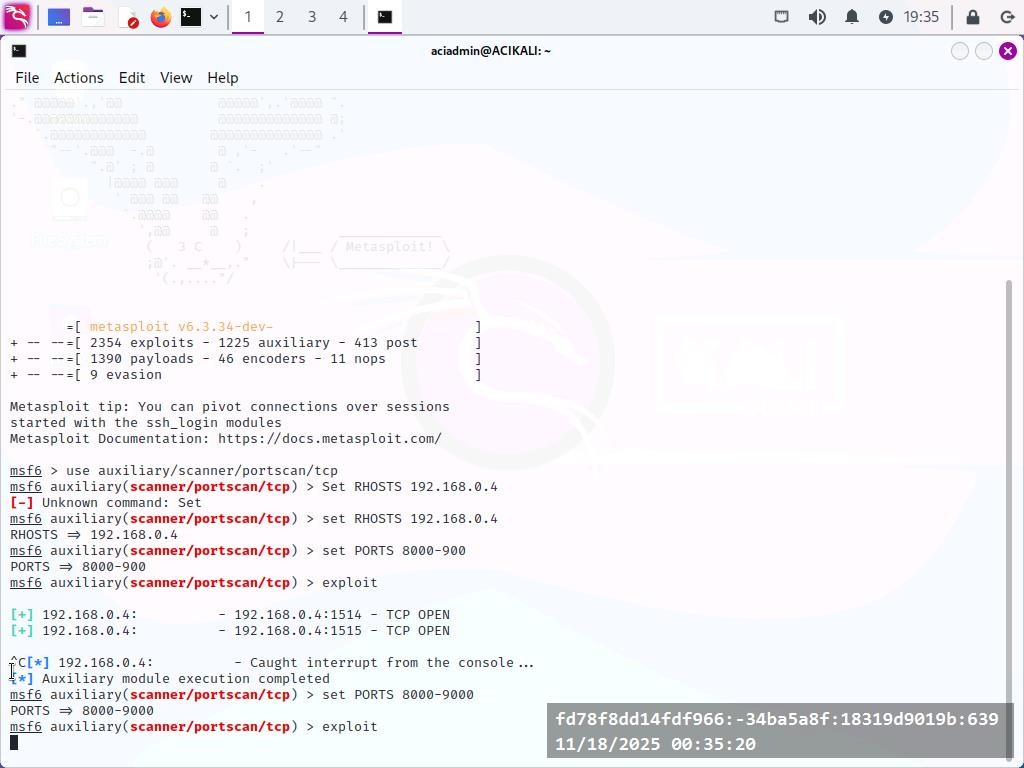
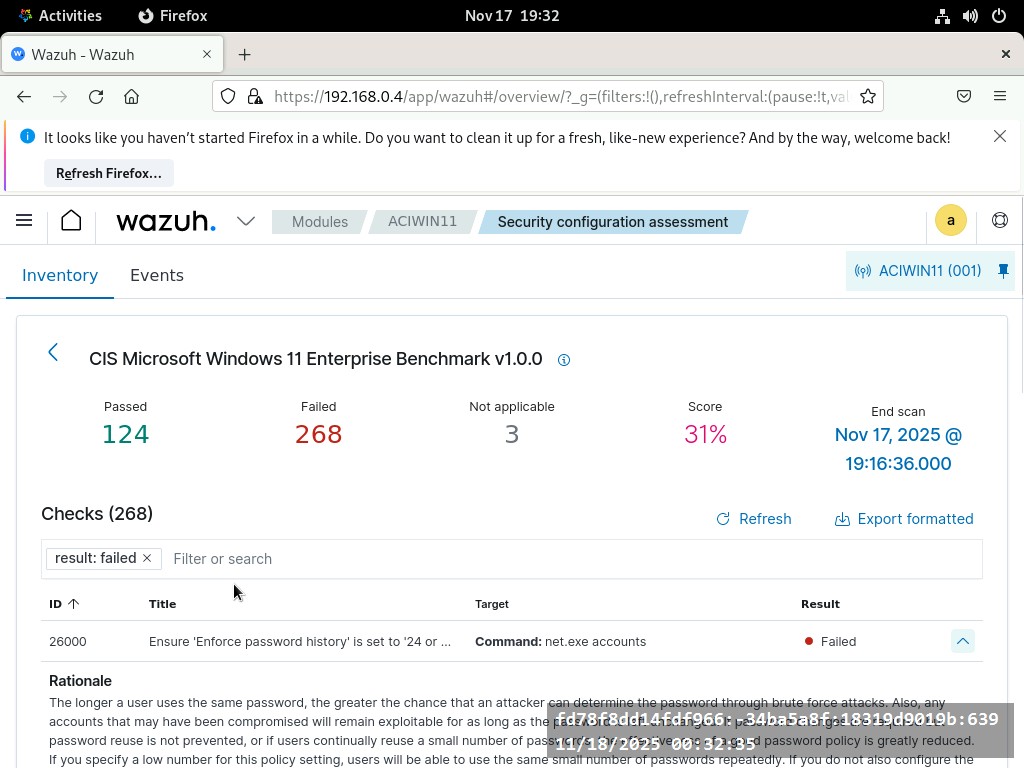
Live Virtual Machine Lab 12-1: Vulnerability Management
While there where a variety of hands on labs that have helped in strengthening my hands on skillset within the course, one of the most critical ones was vulnerability management. This lab exposed me to various actives that are associated with vulnerability management, including identification methods, analysis, vulnerability response and remediation, and reporting. This further allowed me to understand the importance of prioritizing vulnerabilities based on the risk they inquire.
Learning reflection:
This assignment allows me to highlight my growth and development throughout the course, the challenges that I overcame throughout the course and how I pushed pass them, and finally how I can use what I learned throughout this course professionally and academically.
Project/Research showcase
This paper looks to highlight the importance of blockchain technology, and why it is crucial within the field of cybersecurity, but more importantly the way in which it can aid in cyber defense. This paper highlights may key areas in which original defense systems lack the proper measures, but Blockchain systems can help in mitigating this issue.