Cybersecurity isn’t just about theory but also knowing how to use the right tools to detect, analyze, and respond to real threats. Through my experience, I’ve developed strong hands-on skills with tools like Wireshark, Snort, and basic phishing analysis techniques. This skill is showcased in a mock phishing scenario where I analyzed a suspicious email, examined the network traffic using Wireshark, and created a Snort rule to detect and alert on access to the phishing site. These artifacts reflect my ability to apply classroom knowledge to simulated threat environments, reinforcing the technical precision needed in real-world cybersecurity operations.
The first artifact is phishing email analysis of a mock phishing email. It was examined for red flags including suspicious sender domains, misleading language, and embedded links. This analysis demonstrates my ability to spot social engineering tactics and identify phishing attempts before they escalate.
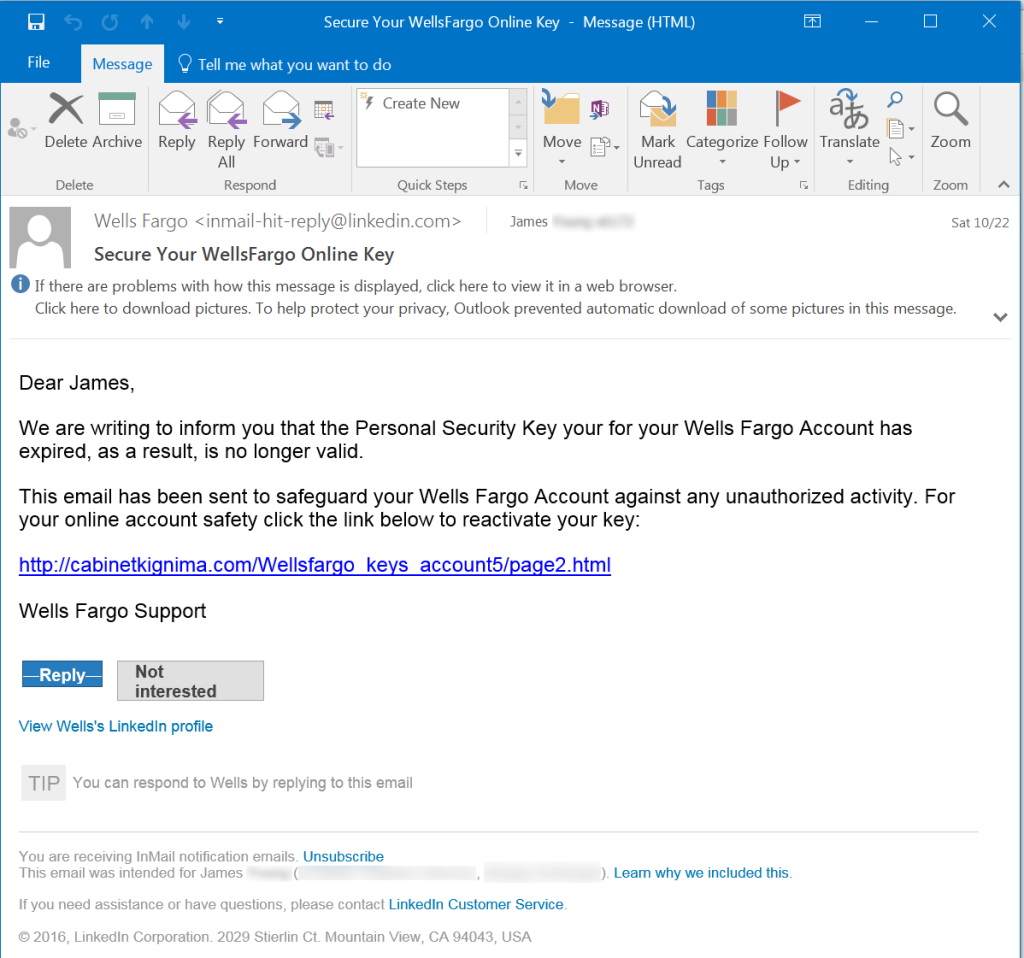
Here is the step by step on me working an alert with this email.
- I typically start by inspecting the email headers and content for red flags. I can see that the email says its from Wells Fargo but email address does not match as its really from ‘inmail-hit-reply@linkedin.com‘
- I spotted a gramatical error in the first sentence. This is common in social engineering schemes however recently the use of AI has minimized errors msking malicious emails a bit harder to spot.
- The reactivation key link is also not a Wells Fargo domain. That’s a tall tale sign its a credential harvester link. Credential harvesting is a common tactic used in phishing attacks, where unsuspecting users are tricked into entering their usernames and passwords into malicious websites.
- I would use an offline malware machine and trace any links to see where they lead.
- I then check the domain reputation and look for indicators of compromise (IOCs) such as IP addresses or hostnames. Finally, I document the findings, escalate if needed, and apply detection rules to help prevent future attacks. This mock investigation demonstrates my understanding of the phishing kill chain and how to identify and respond to credential-based threats.
For my artifact two, using Wireshark, (a free and open-source network protocol analyzer used to capture and inspect data packets traveling over a network), I analyzed network traffic triggered by the phishing link, capturing a POST request that sent credentials from a fake login form on www[.]cabinetkignima[.]com to a harvesting script (login.php). This exercise displays my skills in packet inspection and highlighted how attackers exfiltrate data over unsecured channels emphasizing the value of traffic analysis in detecting threats early.
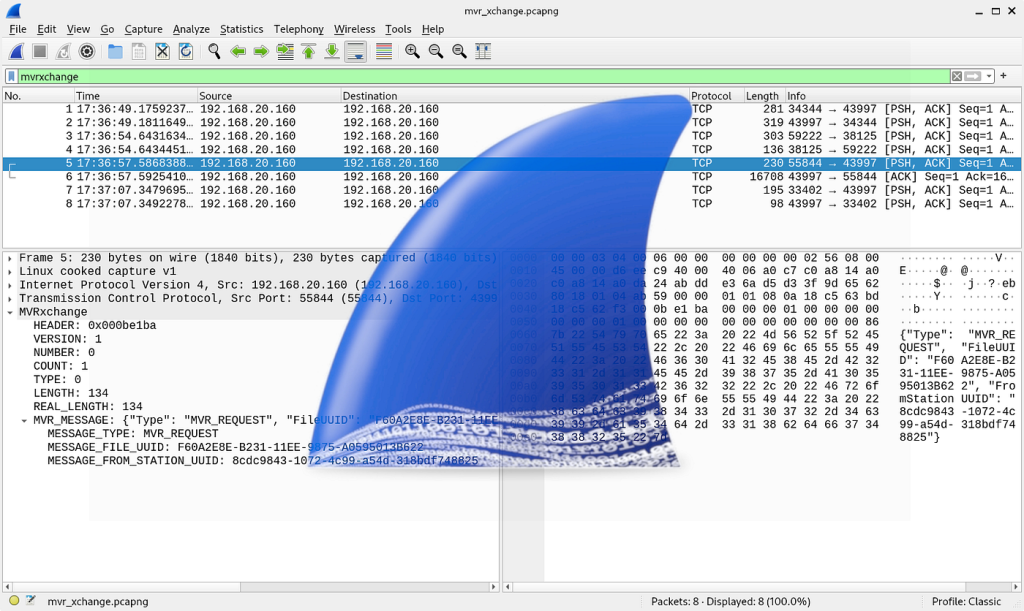
POST /login.php HTTP/1.1
Host: www[.]cabinetkignima[.]com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,/;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://mail.example.com/login
Content-Type: application/x-www-form-urlencoded
Content-Length: 42
Connection: keep-alive
username=jsmith%40gmail.com&password=pass1234
For final artifact, I wrote a Snort IDS rule designed to detect and alert on traffic to the phishing domain. This exercise showcases my understanding of signature-based detection, rule syntax, and practical threat mitigation using intrusion detection tools.
Snort Alert: Possible Phishing Attempt Detected
This Snort rule is designed to detect traffic to the known phishing domain used for credential harvesting we discovered earlier.
alert tcp any any -> any 80 (msg:"Phishing Credential Harvester Site Detected"; content:"www.cabinetkignima.com"; http_host; sid:100001;)
Description of rule
- Monitors all outbound HTTP traffic on port 80.
- Triggers an alert when a request is made to www.cabinetkignima.com, a phishing site hosting a fake login page.
- Identifies potential credential exfiltration attempts from compromised hosts.
This rule demonstrates my ability to write and implement Snort intrusion detection signatures tailored to real-world threats. It required understanding how Snort processes HTTP traffic and how to use content matching to detect malicious domains.
Working on this rule helped reinforce my understanding of phishing techniques, packet inspection, and threat detection using network security tools. It also gave me hands-on experience applying defensive strategies in a lab environment, which I can carry forward into professional practice.
