BLUF
SCADA systems monitor and control water treatment plants, energy systems, and transportation networks. These systems help organizations handle large industrial operations, but they can also make them more vulnerable to cyberattacks if not adequately protected. Knowing SCADA systems’ weaknesses is crucial because attacks on them could disrupt vital services.
Introduction
A lot of the good infrastructure of today is due to technology. Some of the systems that industrial control systems (ICS) are used to run include power grids, water treatment plants, oil pipelines, and transportation networks. One of the most popular types of ICS is the Supervisory Control and Data Acquisition (SCADA) system. SCADA lets people control processes remotely, gather data from sensors, and monitor machines. These systems help companies run complicated factory tasks over large areas.
Components of SCADA Systems
There are a few important parts of SCADA systems that let them keep an eye on and control infrastructure. The Human Machine Interface (HMI) is an important part that lets operators see system data and talk to the system. The Remote Terminal Unit (RTU) is another part. It gets data from physical devices like sensors and turns it into digital data. People also often use programmable logic controllers (PLCs) to run machines and processes in factories. These parts talk to a central supervisory system that collects and analyzes the data that is being made. These technologies work together to let businesses keep an eye on their operations and make changes when they need to (SCADA Systems, n.d.).
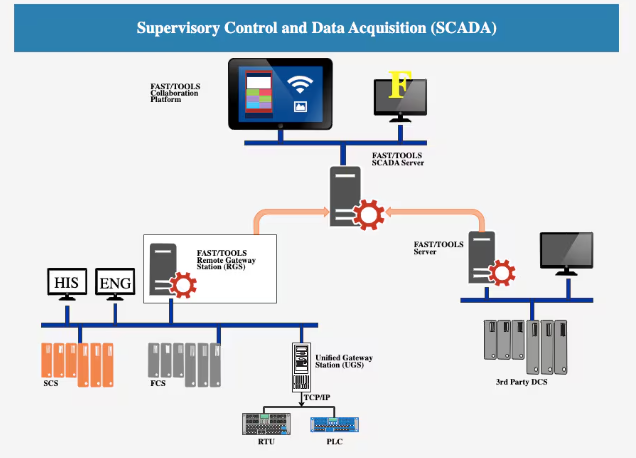
Figure 1. This image shows how SCADA systems connect sensors, controllers, and central servers to monitor and control critical infrastructure operations.
Vulnerabilities in SCADA Systems
SCADA systems are very useful, but they also make it easier for hackers to get into systems. Many SCADA systems were made to be reliable and efficient, not secure. This is why some systems don’t have good authentication or encryption features. If attackers gain access to these networks, they may be able to manipulate industrial equipment or disrupt important services. For instance, cyberattacks on water or energy systems could cause big problems for communities. When SCADA systems are linked to corporate networks or the internet, they are also open to attack. More connections make communication and productivity better, but they also make it easier for hackers to attack. Attackers may try to get into critical infrastructure networks by taking advantage of weak network protections, old software, or systems that aren’t set up correctly (Stouffer, Falco, & Scarfone, 2015).
Role of SCADA in Risk Mitigation
Even with these weaknesses, SCADA systems help businesses find and fix problems quickly. These systems let you watch things in real time and send you alerts when something goes wrong. For instance, if a sensor detects unusual pressure in a pipeline or temperature in a power plant, the SCADA system can alert operators right away. Organizations can further reduce their risk by using cybersecurity tools such as firewalls, network segmentation, intrusion detection systems, and secure communication protocols. These protections help keep SCADA systems running safely by preventing unauthorized people from getting in.
Conclusion
Managing modern infrastructure would be very difficult without SCADA systems. They help businesses monitor industrial processes and fix problems quickly when they occur. But these systems also carry cybersecurity risks that need careful handling. Cybersecurity experts will still need to protect SCADA systems from cyber threats as infrastructure becomes more connected and advanced.
References
SCADA Systems. (n.d.). Supervisory Control and Data Acquisition systems overview. Course reading. Stouffer, K., Falco, J., & Scarfone, K. (2015). Guide to Industrial Control Systems (ICS) Security (NIST Special Publication 800-82). National Institute of Standards and Technology.