The CIA Triad—Confidentiality, Integrity, and Availability—is foundational to cybersecurity and
is a key concept for companies seeking to protect their information systems (Chai, 2022).
Authentication and authorization are two different processes that help protect the CIA Triad.
They work by verifying a user’s identity and then deciding who can access certain resources.
Together, these processes support modern information security.
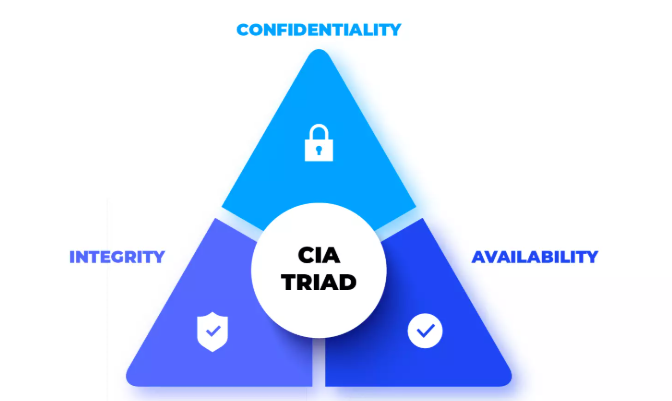
Figure 1. This diagram represents the three core principles of cybersecurity: confidentiality, integrity, and availability.
Authentication is the process of verifying whether a user is who they claim to be. It confirms a
person’s identity and can be done using usernames and passwords, PINs, biometric scans,
security tokens, or two-factor authentication. For example, logging into a university’s learning
management system is a form of authentication.
Authorization
Authorization decides what an authenticated user can and cannot do. It determines what a user is
allowed to access after their identity has been verified. Authorization controls include file
permissions, role-based access control (RBAC), and access control lists. For example, after
logging into Canvas, a student can view assignments and submit work, but they cannot edit
course content because they are not authorized to do so.
The Most Important Difference
The primary difference between authentication and authorization is that authentication confirms
identity, while authorization grants access. Authentication is always the first step. A user must be
properly authenticated before authorization can occur.
Conclusion
The CIA Triad is an important part of designing and understanding a cybersecurity plan.
Confidentiality protects private information, integrity ensures data accuracy, and availability
ensures systems remain accessible when needed. Authentication and authorization support these
ideas by verifying user identity and setting appropriate access controls. As the world becomes
increasingly digital, these concepts work together to help organizations build information
systems that are secure, reliable, and trustworthy.
References
Chai, W. (2022). What is the CIA triad? Definition, explanation, examples. TechTarget.
https://www.techtarget.com/whatis/definition/Confidentiality-integrity-and-availability-CIA