This artifact demonstrates my ability to analyze network reconnaissance activity and implement defensive security controls. In this assignment, I used tools such as Nmap and Wireshark to observe how attackers gather information about network systems. By performing an aggressive Nmap scan across several virtual machines, I was able to identify open ports, services, and operating system information associated with each host. This process illustrates how attackers conduct reconnaissance to locate potential vulnerabilities within a network.
During the analysis, I also used Wireshark to monitor traffic patterns generated by the scan. The captured packets revealed common reconnaissance indicators such as ICMP echo requests, TCP SYN packets, and SYN-ACK responses, which are used to discover active hosts and identify open ports. Observing these patterns helped me understand how network scanning activity appears from the defender’s perspective and how monitoring tools can be used to detect suspicious behavior. In addition to analyzing network traffic, I configured pfSense firewall rules to block ICMP traffic and restrict unauthorized communication from an external system. This defensive configuration demonstrates how security professionals can limit attack surfaces and prevent reconnaissance attempts from reaching internal systems.
Overall, this artifact highlights my developing skills in network monitoring, vulnerability assessment, and defensive security configuration, which are essential for protecting systems against cyber threats.
Artifact 1
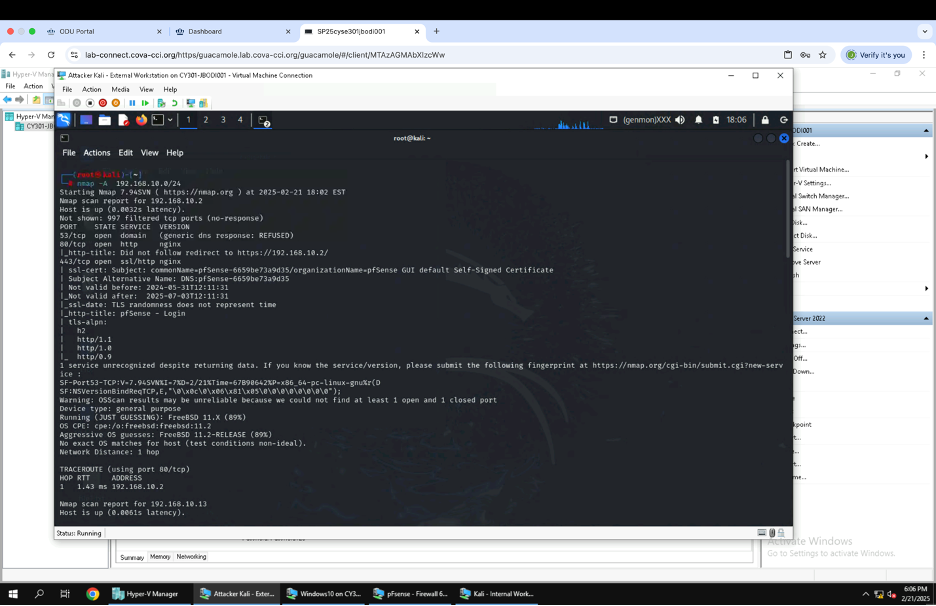
Figure showing the use of Nmap to profile the basic information about the subnet topology (including open ports information, operating systems, etc.) from an aggressive scan on internal Kali.
Artifact 2
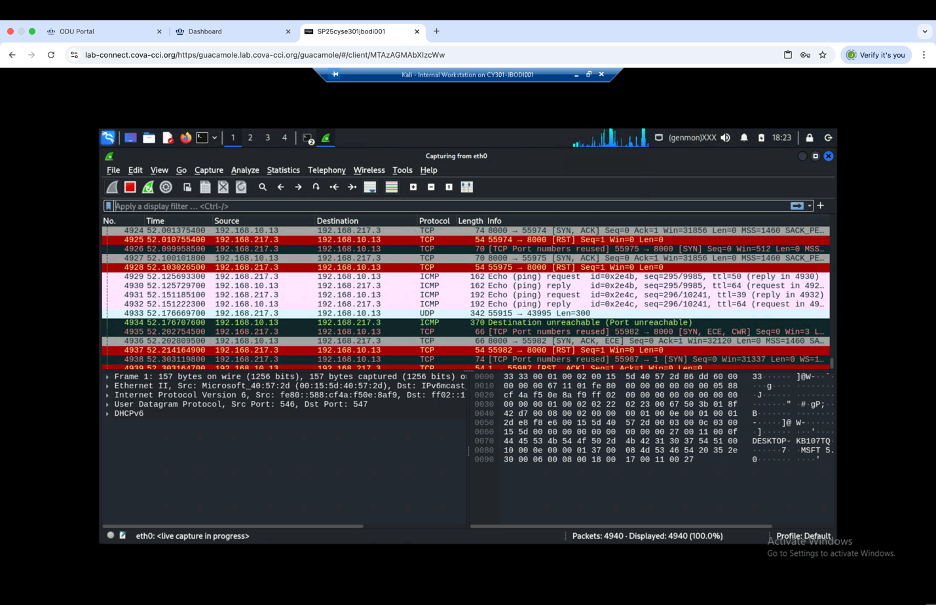
Using Wireshark on the internal Kali virtual machine while the external Kali virtual machine scans the network using NMAP reveals distinct traffic patterns associated with packet sniffing/reconnaissance activities. In the captured packets, several indicators of network scanning were observed, including ICMP Echo requests, TCP SYN packets, and reset (RST) responses. The presence of multiple ICMP Echo (ping) requests indicates that the scanning system is performing a network discovery to identify active hosts. Additionally, numerous TCP SYN packets targeting different ports, particularly common service ports like 8000, suggest a SYN scan, a technique used to determine open ports on a target system. The corresponding TCP RST packets imply that the destination ports are closed, rejecting the connection attempts. In addition to ICMP, the scan revealed a number of TCP SYN requests indicating part of a 3-way handshake process. Each SYN packet represents an attempt to establish a connection with a specific port. Another significant finding is the appearance of TCP SYN-ACK responses, which show open ports and indicate potential attack surfaces. The captured packets also include “Destination Unreachable” ICMP responses, suggesting that some hosts or services are unavailable. This traffic pattern strongly suggests that the external Kali system is conducting an aggressive scan using Nmap. The data highlights the importance of network monitoring in detecting reconnaissance activities, which are often precursors to cyber-attacks.
Artifact 3
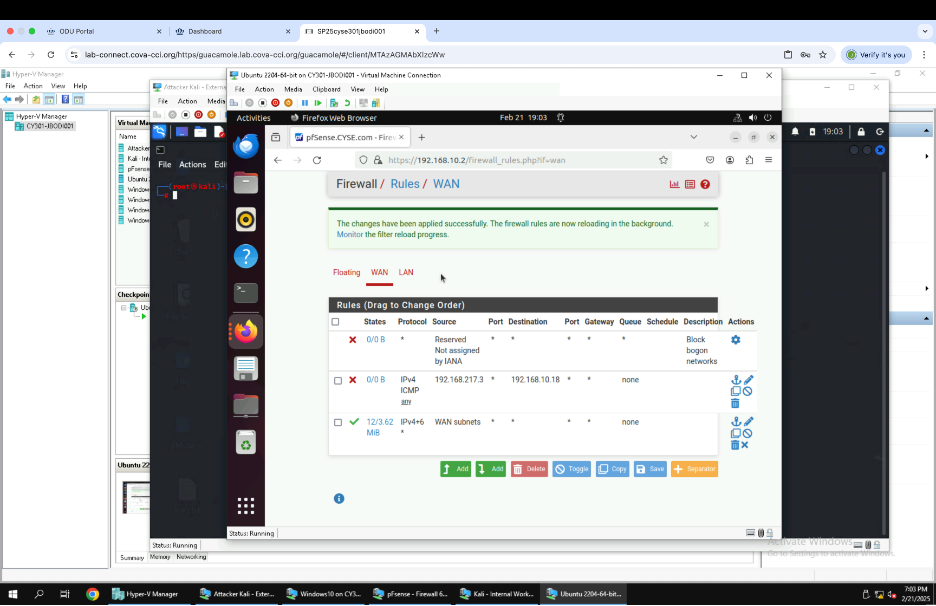
Figure showing the Pfsense firewall configured to block all ICMP packets from the source External Kali VM to the destination Ubuntu VM
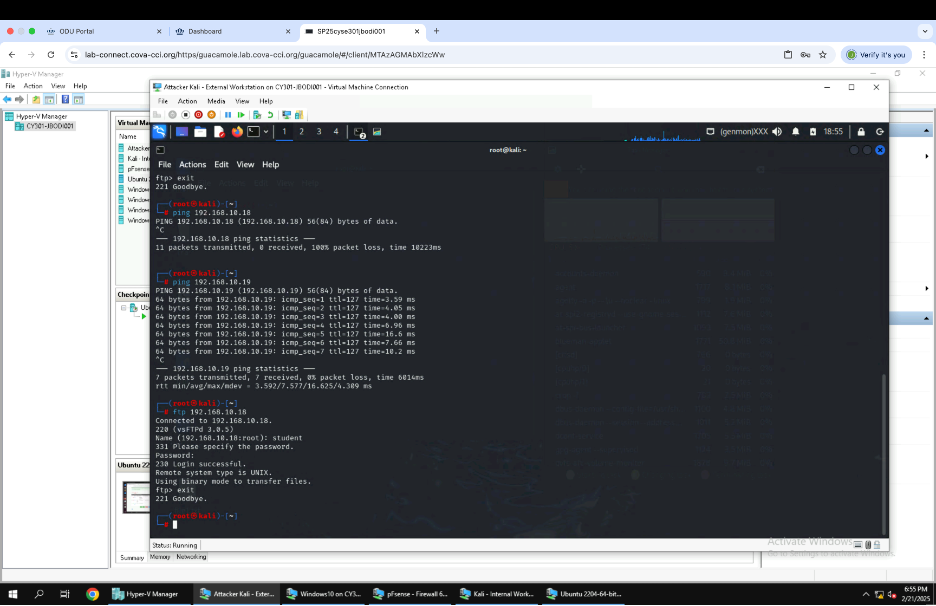
Figure showing ICMP packets being blocked from external Kali VM to ubuntu VM.